Review Windows Server 2012r2 What Are Some of the Key Remote Access Services
The Configure Network Services and Admission domain is another with simply one objective tested on the seventy-417 exam: Configure DirectAccess.
DirectAccess is an improved alternative to a VPN that was first introduced in Windows Server 2008 R2 and Windows 7. If y'all earned your Windows Sever 2008 MCSA before the release of Windows Server 2008 R2, you might have missed this major new applied science completely. And if y'all did learn about DirectAccess in Windows Server 2008 R2, yous need to know that this feature has changed significantly in Windows Server 2012 and Windows Server 2012 R2.
Objectives in this chapter:
- Objective 6.ane: Configure DirectAccess
Objective 6.one: Configure DirectAccess
DirectAccess in Windows Server 2008 R2 and Windows 7 was a very promising technology that was as well hard to configure. Showtime with Windows Server 2012 and Windows eight, the infrastructure requirements of DirectAccess have been simplified forth with the configuration steps. At the same time, its characteristic set has expanded considerably.
For the 70-417 test, you offset demand to understand basic DirectAccess concepts and components. You likewise need to know how the infrastructure requirements to back up DirectAccess clients differ to support various features. Finally, you need to know how to configure DirectAccess.
What is DirectAccess?
DirectAccess is an ever-on remote access technology that is based on IPv6 communication. Through DirectAccess, a user's figurer automatically, transparently, and deeply connects to a individual corporate network from whatever location in the earth equally presently every bit the computer is connected to the Internet. When a DirectAccess connection is active, remote users connect to resource on the corporate network as if they were on the local premises.
DirectAccess overcomes the limitations of VPNs by providing the following benefits:
- Always-on connectivity Unlike with a VPN, a DirectAccess connexion is ever on, even before the user logs on to his or her computer.
- Seamless connectivity To the user, the DirectAccess connection to the corporate network is completely transparent and resembles an always-on VPN connection.
-
Bidirectional access With DirectAccess, the user's remote computer not only has access to the corporate intranet, simply the intranet tin can also see the user'southward computer.. This means that the remote computer can be managed by using Group Policy and other management tools (such as System Center 2012 R2 Configuration Manager ["Configuration Director" for short]) in exactly the aforementioned way that computers located on the internal network are managed.
In addition, DirectAccess includes the following security features:
- DirectAccess uses IPsec to cosign both the calculator and user. If you want, you tin can crave a smart card for user authentication.
- DirectAccess also uses IPsec to provide encryption for communications across the Cyberspace.
Understanding IPv6 and DirectAccess
A DirectAccess connection from a remote client to an internal resource includes two legs. In the start one-half of the connection, the DirectAccess client always uses IPv6 to initiate contact with the DirectAccess server, typically found at the border of the private network. IPv6 transition technologies are used to assistance this connexion when necessary. The 2nd one-half of the connexion occurs between the DirectAccess server and the internal network resources. This part of the connexion tin can proceed either over IPv4 (only if the DirectAccess server is running Windows Server 2012 or Windows Server 2012 R2 and acting as a NAT64/DNS64 device) or over IPv6.
Figure 6-1 shows the two legs of a DirectAccess connection between a remote client and an internal network resource.
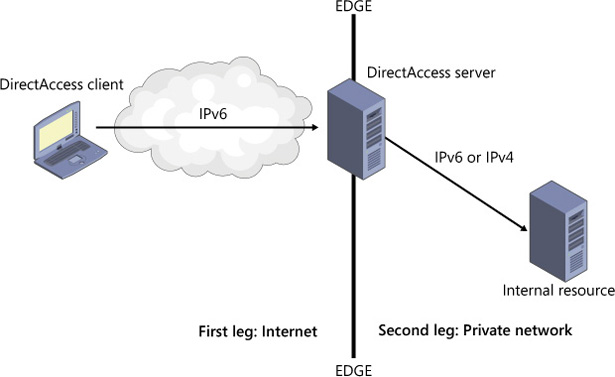
Figure 6-one A DirectAccess connection to an internal resource
First leg: External customer to private network edge
If the DirectAccess client can obtain a global IPv6 address from its surround, so the connection to the DirectAccess server proceeds over the IPv6 Internet in a straightforward mode. However, IPv6 is non widely implemented yet on public networks, so iii IPv6 transition technologies are used to help in establishing the IPv6 connexion to the DirectAccess server. If all three of the following transition technologies are enabled on the client through Group Policy, they are attempted in the post-obit society of preference:
- 6to4 For DirectAccess clients that have a public IPv4 address, 6to4 can be used to connect to the DirectAccess server via IPv6 beyond the public IPv4 Cyberspace. 6to4 achieves this by tunneling or encapsulating IPv6 data within an IPv4 header, in a technique known equally IPv6-over-IPv4. 6to4 requires whatsoever intervening router or firewall to be configured so that outbound traffic for Protocol 41 is allowed. As well note that 6to4 does not piece of work if the client is backside a network address translation (NAT) device.
- Teredo For DirectAccess clients behind a NAT device and configured with a private IPv4 address, Teredo tin can be used to connect to the DirectAccess server via IPv6 across the public IPv4 Internet. Similar 6to4, Teredo tunnels IPv6 traffic in IPv4. The intervening routers and firewalls must be configured to let outbound traffic through User Datagram Protocol (UDP) port 3544.
- IP-HTTPS For DirectAccess clients that cannot effectively establish IPv6 connectivity to the DirectAccess server through 6to4 or Teredo, IP-HTTPS is used. With IP-HTTPS, DirectAccess clients encapsulate IPv6 traffic within HTTPS traffic. Nigh all routers allow outbound HTTPS traffic, so this choice is almost always possible.
2nd leg: Individual network edge to internal resource
Between the network edge and the internal network resource, the connexion can proceed over either IPv6 or IPv4. You don't take to deploy global IPv6 on your internal network because Windows Server 2012 and Windows Server 2012 R2 can act as a NAT64/DNS64 device when deployed equally a DirectAccess server at the network border. (A NAT64/DNS64 device translates between IPv6 and IPv4.) Withal, an all-IPv6 connection still provides the best performance and is the preferred scenario.
Understanding the DirectAccess connection process
A DirectAccess connection to a target intranet resource is initiated when the DirectAccess client connects to the DirectAccess server through IPv6. IPsec is so negotiated between the client and server. Finally, the connection is established between the DirectAccess customer and the target resource.
This full general process can exist summarized in the post-obit steps:
-
The DirectAccess customer computer attempts to connect to an internal reckoner configured equally the network location server. If the network location server is available, the DirectAccess customer determines that it is already connected to the intranet, and the DirectAccess connection process stops. If the network location server is not available, the DirectAccess customer determines that information technology is continued to the Internet and the DirectAccess connectedness procedure continues.
- The DirectAccess client reckoner connects to the DirectAccess server by using IPv6 and IPsec. If a native IPv6 network isn't available, the client establishes an IPv6-over-IPv4 tunnel by using 6to4, Teredo, or IP-HTTPS. The user does not take to be logged in for this stride to consummate.
- Equally office of establishing the IPsec session, the DirectAccess customer and server authenticate each other past using Kerberos or estimator certificates.
- By validating Active Directory Domain Services grouping memberships, the DirectAccess server verifies that the estimator and user are authorized to connect using DirectAccess.
- If Network Access Protection (NAP) is enabled and configured for health validation, the DirectAccess client obtains a health certificate from a Health Registration Authority (HRA) located on the Internet prior to connecting to the DirectAccess server. The HRA frontward the DirectAccess client's health condition information to a NAP health policy server. The NAP wellness policy server processes the policies defined inside the Network Policy Server (NPS) and determines whether the client is compliant with system health requirements. If so, the HRA obtains a health certificate for the DirectAccess customer. When the DirectAccess client connects to the DirectAccess server, it submits its health certificate for authentication.
- The DirectAccess server begins forwarding traffic from the DirectAccess customer to the intranet resources to which the user has been granted access.
Understanding DirectAccess infrastructure options
You can deploy DirectAccess in a number of network scenarios, ranging from the very simple to the very complex. A few of these options are illustrated in the examples that follow.
Simple DirectAccess infrastructure
A unproblematic DirectAccess infrastructure includes a DirectAccess server that is running Windows Server 2012 or Windows Server 2012 R2 and is deployed at the network border. This DirectAccess server is configured every bit a Kerberos proxy and NAT64/DNS64 translation device. The external interface is configured with a public IP address. (Ii would be necessary to support Teredo.) The internal address is associated with the network location server.
Within the internal network is a domain controller/DNS server and at least one internal network resource such as a file server or application server. Note that this elementary infra-structure supports only Windows 8 clients and later on because Windows 7 clients practise not support Kerberos authentication for DirectAccess.
Figure 6-ii shows a unproblematic DirectAccess infrastructure.
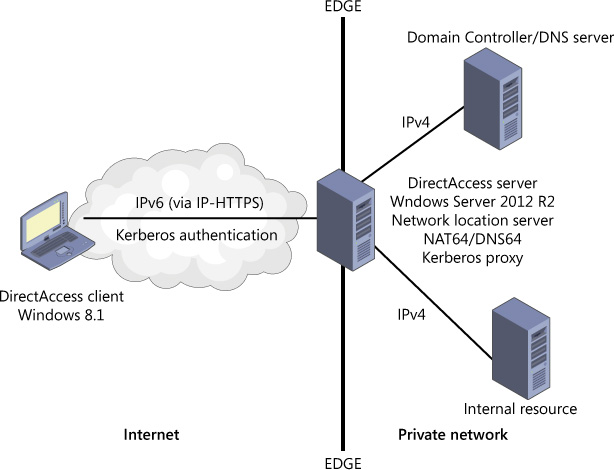
FIGURE half-dozen-2 A uncomplicated DirectAccess infrastructure
DirectAccess server backside NAT
Showtime with Windows Server 2008 R2, all versions of DirectAccess allow y'all to deploy a DirectAccess server behind the network edge in a perimeter network. However, only in Windows Server 2012 and Windows Server 2012 R2 tin can you deploy the DirectAccess server behind a NAT device. In such a scenario, the DirectAccess server needs merely a unmarried network adapter and a single address. Connections from the DirectAccess clients through the NAT device to the DirectAccess server are established through IP-HTTPS.
Figure 6-3 illustrates a DirectAccess network topology in which a DirectAccess server is deployed behind a NAT device.
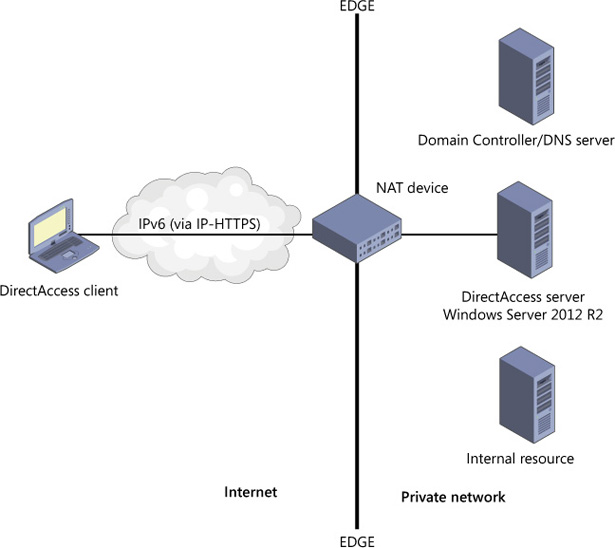
FIGURE vi-3 DirectAccess server deployed behind a NAT device
Multisite/Multidomain DirectAccess infrastructure
Some other infrastructure pick that is new to Windows Server 2012 and Windows Server 2012 R2 is the ability for DirectAccess to exist deployed beyond multiple sites. A multisite deployment of DirectAccess requires a public key infrastructure (PKI) and computer authentication through certificates. In addition, multidomain back up is at present a built-in feature of DirectAccess that requires no extra configuration.
When yous configure a multisite deployment, the DirectAccess clients are provided with a list of the DirectAccess servers that act every bit entry points to the private network at each site. Before connecting, DirectAccess clients running Windows eight or afterward and then ping each of these DirectAccess servers. The Windows 8 or later client then initiates contact with the server whose latency is determined to exist the shortest. (Windows vii clients in a multisite deployment simply utilise a unmarried, preconfigured DirectAccess server address.)
Figure half-dozen-4 shows a multisite DirectAccess infrastructure.
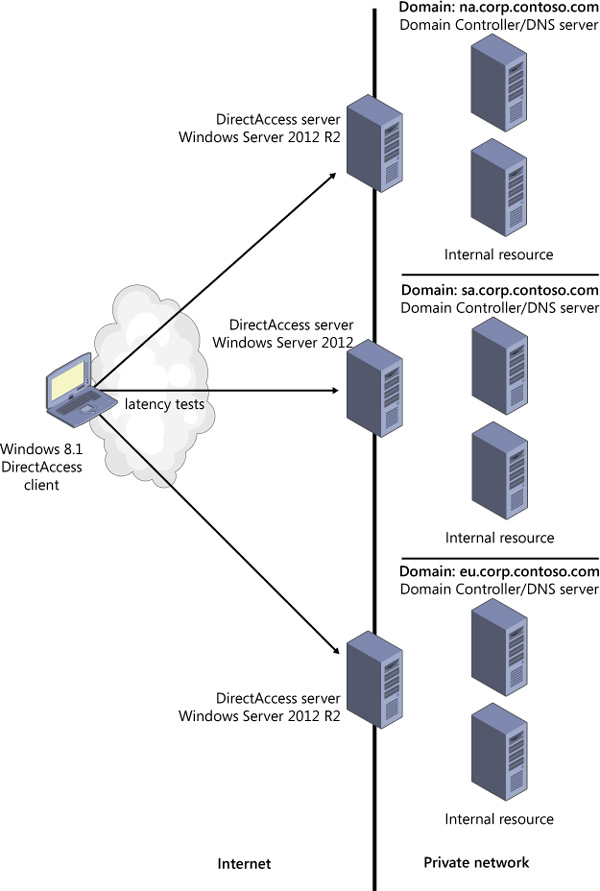
Figure 6-4 A multisite DirectAccess infrastructure
Complex DirectAccess infrastructure
Although Windows Server 2012 and Windows Server 2012 R2 greatly simplify the basic infrastructure requirements for DirectAccess, the infrastructure can get complex if you lot need functionality that is not included by default in a basic setup. For example, one new feature introduced in Windows Server 2012 is the ability to deploy DirectAccess servers in a Network Load Balancing (NLB) cluster. This functionality naturally adds complexity to your infrastructure only is often necessary to support many remote clients. Another requirement that adds more elements to your infrastructure is the need to support Windows 7 clients. Windows 7 clients can authenticate DirectAccess connections only with computer certificates, so your DirectAccess infrastructure would crave a PKI in such a scenario. Next, DirectAccess tin also be deployed with NAP, which is some other factor that adds complication but might be required past your Information technology policies. Additional features such every bit two-factor hallmark with one-time passwords (OTPs) would raise the infrastructure requirements fifty-fifty more than. Figure half-dozen-5 illustrates a more circuitous DirectAccess infrastructure that supports all three IPv6 transition technologies, improves load capacity with an NLB cluster, supports Windows 7 clients with a PKI/certification authority, includes a NAP infrastructure, and has a network location server deployed apart from the DirectAccess server.
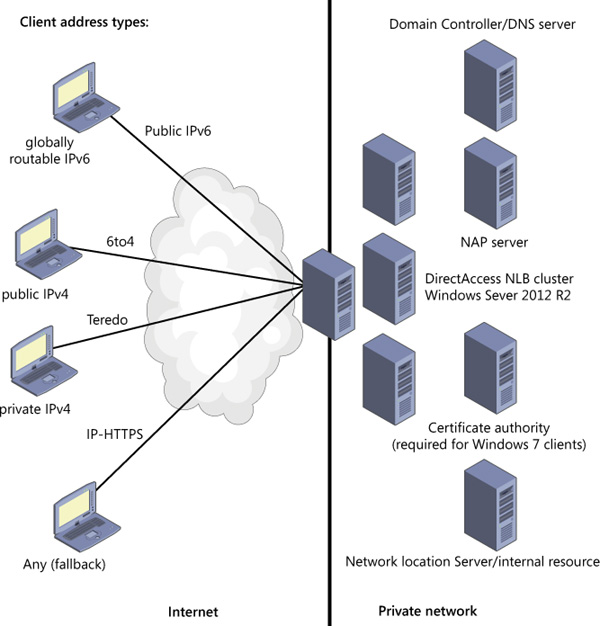
FIGURE half-dozen-5 A complex DirectAccess infrastructure
Installing and configuring DirectAccess
Windows Server 2012 and Windows Server 2012 R2 have greatly simplified the process of installing and configuring DirectAccess. DirectAccess is now unified with traditional VPNs in a new Remote Admission server role and managed with the aforementioned tool, the Remote Access Management Console. In fact, you tin can now configure a Windows Server to act every bit both a DirectAccess server and a traditional VPN server at the same time, an selection that was not possible in Windows Server 2008 R2. Even more than significant than unified management are the new configuration wizards offset introduced in Windows Server 2012 that brand the procedure of deploying and configuring DirectAccess and VPNs relatively easy.
Installing DirectAccess
DirectAccess at present belongs to the Remote Access server role. You can install the DirectAccess component of the Remote Access role through the Add Roles and Features Wizard or by typing the following at an elevated Windows PowerShell prompt:
Install-WindowsFeature DirectAccess-VPN -IncludeManagementTools
Yous can and then configure DirectAccess using the Remote Access Management Console, shown in Figure 6-six, or by using Windows PowerShell commands.
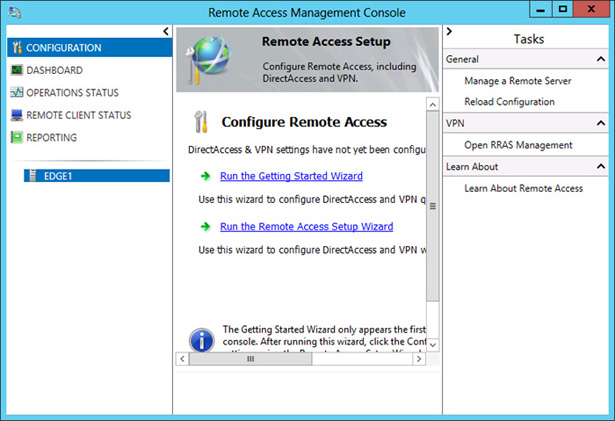
Figure half dozen-6 The Remote Access Management Panel provides a unified configuration and direction tool for all remote access technologies
Configuring DirectAccess
Effigy half dozen-6 shows the Remote Access Management Console before you take whatever configuration steps. The fundamental pane shows two options for wizards: the Getting Started Wizard and the Remote Admission Setup Magician. Whichever magician y'all cull to begin configuration, you are next presented with an option to configure just DirectAccess, just a VPN, or both, as shown in Figure 6-7.
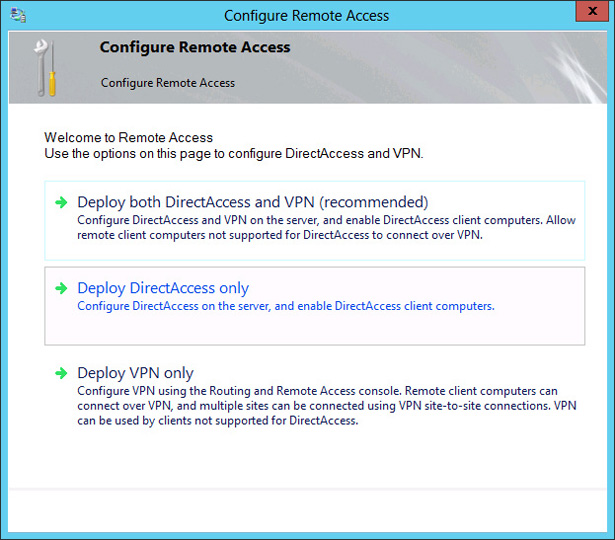
FIGURE six-7 The Remote Access configuration wizards allow you lot to configure just DirectAccess, just a VPN, or both.
The Getting Started Wizard, which was commencement introduced in Windows Server 2012, is an excellent tool that helps you deploy a remote access solution chop-chop. However, it is not particularly useful for exam training precisely because information technology hides the very configuration options y'all need to know and sympathise for the examination. In add-on, VPN configuration has not changed since y'all earned your Windows Server 2008 MCSA in any style that is meaning for the lxx-417 examination. For these reasons, to prepare for the Configure DirectAccess objective for the 70-417 exam, y'all should focus on configuration options that appear after y'all click Run The Remote Access Setup Wizard shown in Effigy 6-half-dozen and so click Deploy DirectAccess Only shown in Figure 6-7.
Later you click Deploy DirectAccess Only, the Remote Access Management Console reappears with the center pane replaced by an epitome like to the one shown in Figure 6-eight. The iv steps in the map are associated with four configuration wizards that you must complete in order: The first is for configuring DirectAccess clients, the second is for configuring the DirectAccess server, the third is for configuring infrastructure servers, and the fourth is for configuring the application servers (if desired). These wizards create and configure Group Policy Objects (GPOs) for DirectAccess servers and clients.
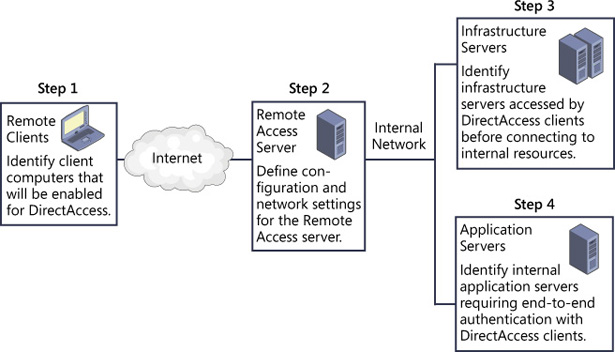
FIGURE six-8 The four DirectAccess configuration wizards
It's unlikely you'll be asked to identify any of these wizards past name on the 70-417 examination. However, yous might be asked about whatever configuration choice that appears in whatsoever of these four wizards. These four wizards, then, provide a useful way to organize the new configuration options that yous need to larn and sympathise for the 70-417 exam, so we will wait at them in society.
Step ane: DirectAccess Client Setup
The first folio of the DirectAccess Customer Setup Wizard is shown in Figure 6-9. This Deployment Scenario page allows you the option to configure DirectAccess clients either for both remote admission and remote direction, or for remote management only. The first, default option configures bidirectional communication for DirectAccess servers and clients. Choosing the second option, however, would permit administrators to manage remote DirectAccess clients through tools such as Configuration Manager, merely it would prevent those clients from accessing the internal corporate network. Note that the choice to deploy DirectAccess clients for remote management merely is new to Windows Server 2012 and Windows Server 2012 R2.
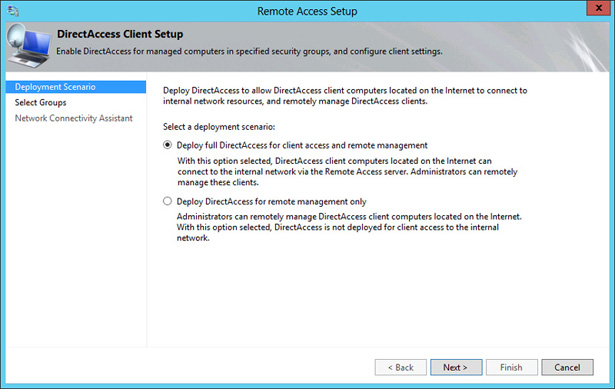
Effigy half dozen-9 The Deployment Scenario page of the DirectAccess Customer Setup Wizard
The 2nd folio of the DirectAccess Client Setup Wizard is the Select Groups page, shown in Figure half-dozen-10. The commencement office of this page is to let you specify the security groups containing the computer accounts that yous desire to enable for DirectAccess. This is an important step to remember: No DirectAccess customer is immune admission to the internal network if you don't assign that client the right to do so. To perform this task in Windows PowerShell, use the Add together-DAClient cmdlet with the -SecurityGroupNameList parameter.
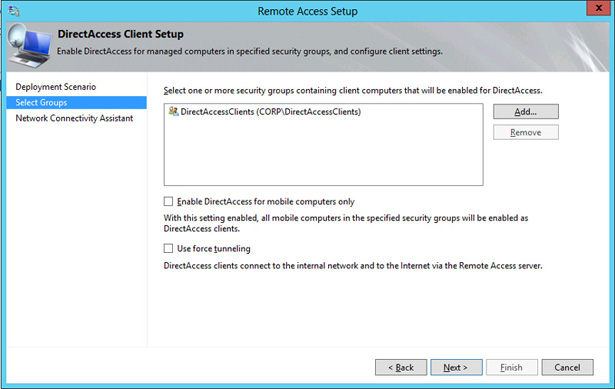
FIGURE half dozen-10 The Select Groups page of the DirectAccess Client Setup Wizard
A second option on this page is to enable DirectAccess for mobile computers merely. Interestingly, this selection is selected by default if you lot run the Getting Started Wizard. Computers connecting remotely through DirectAccess are most likely to be mobile computers, merely there are exceptions, and these exceptions could easily grade the premise of an examination question. (Scenario: Some users working on domain-joined desktop computers from remote sites can't connect through DirectAccess. Why non? The pick to enable DirectAccess for mobile computers only is selected.)
The tertiary option on this folio is Use Force Tunneling. This option forces the DirectAccess client to tunnel all network traffic through the private network, regardless of where that traffic is ultimately destined. This beliefs, for example, could be used to ensure that all web traffic from DirectAccess clients passes through an internal web proxy server. In Windows PowerShell, this option is configured by using the Ready-DAClient cmdlet with the -ForceTunnel parameter.
The last folio in the DirectAccess Client Setup Wizard is the Network Connectivity Assistant folio, shown in Figure 6-eleven. The Network Connectivity Banana is client software embedded in Windows 8 and later that determines whether DirectAccess is functioning. (This feature is not the same as the network location server, which helps a client decide whether it is on the Internet or intranet.)
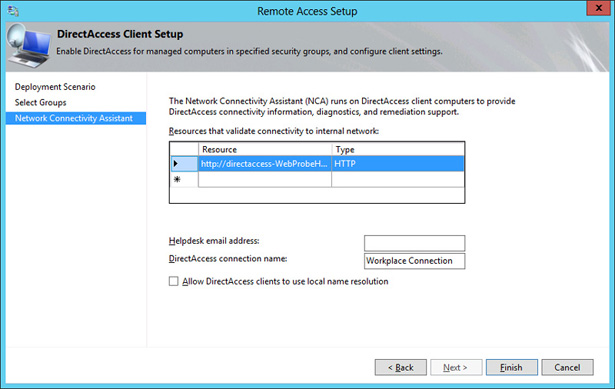
FIGURE 6-11 The Network Connectivity Assistant page of the DirectAccess Client Setup Sorcerer
The first setting on this page is the host address for the Network Connectivity Assistant. DirectAccess customer computers use this address to verify that the customer can successfully connect to the internal network. This setting is unlikely to appear on the 70-417 exam (except perchance as an wrong answer choice), just if you demand to enter this resource manually, you should specify the address of a corporate URL or FQDN that is e'er available to DirectAccess clients. Your internal DNS should resolve this address to the internal address of the Remote Admission server.
The almost testable setting on this page is the choice to permit DirectAccess clients to use local proper name resolution. Local name resolution in this instance refers to the broadcast-based protocols of NetBIOS over TCP/IP and Link-Local Multicast Proper noun Resolution (LLMNR). When this choice is enabled, DirectAccess clients are allowed to resolve unmarried characterization names such as App1 using local name resolution if they can't be resolved through DNS. Local name resolution must also exist configured in the Infrastructure Server Setup Sorcerer.
Step 2: Remote Access Server Setup
The kickoff folio of the Remote Access Server Setup Sorcerer is the Network Topology page, shown in Effigy 6-12. This folio lets you specify where in your network you are going to deploy your DirectAccess server.
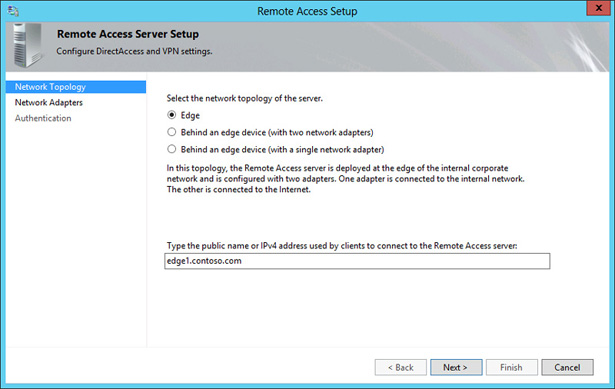
Figure vi-12 The Network Topology page of the Remote Admission Server Setup Wizard
The beginning choice is Border. Choosing this option requires the DirectAccess server to be configured with two network adapters, i connected direct to the Cyberspace and 1 connected to the internal network. The external interface needs to be assigned two consecutive public IPv4 addresses if yous need to support Teredo.
The second option is Behind An Border Device (With Two Network Adapters). Select this selection if you want to deploy the DirectAccess server in a perimeter network behind a firewall or router. In this topology, the network adapter attached to the perimeter network is assigned 1 or two sequent public IPv4 addresses, and the second adapter fastened to the internal network tin be assigned a individual accost.
The tertiary option is Behind An Edge Device (With A Unmarried Network Adapter). Choose this choice if you want to deploy your DirectAccess server behind a NAT device. In this case, your DirectAccess server is assigned a unmarried individual IP address.
Finally, the Network Topology page requires you to specify the proper name or IPv4 accost the DirectAccess clients will use to connect to the DirectAccess server. Be sure to specify a name that tin exist resolved through public DNS or an IPv4 address that is reachable from the public network.
The 2d folio of the Remote Admission Server Setup Wizard is the Network Adapters page, shown in Figure 6-13. This folio requires you to choose the network adapter or adapters that will be assigned to internal network and external network, as required by your specified topology.
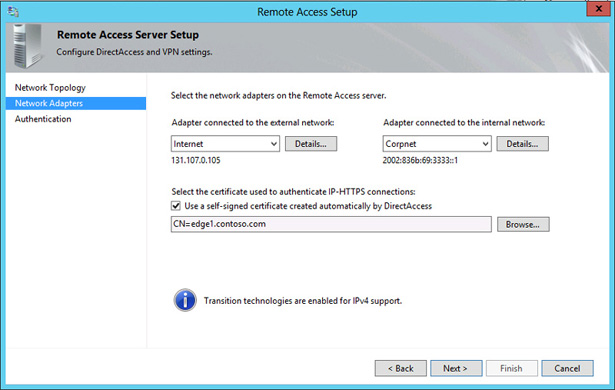
Figure 6-13 The Network Adapters page of the Remote Access Server Setup Wizard
This folio also requires you to specify a certificate that the DirectAccess server volition use to authenticate IP-HTTPS connections. If your organization has deployed a PKI, yous can browse to a copy of the figurer certificate for the local server. If you don't have a PKI, you need to choose the option to utilize a self-signed certificate instead. Note that the availability of this latter option was first introduced in Windows Server 2012 and could easily serve as the basis for a test question.
The concluding page of the Remote Admission Server Setup Magician is the Hallmark folio, shown in Effigy vi-14. This folio lets you configure the following settings related to DirectAccess client authentication:
-
User Authentication By default, users authenticate simply with Agile Directory credentials. However, y'all can choose the option here to require 2-gene authentication. Typically, two-factor authentication requires a user to insert a smart card in addition to typing his or her Active Directory credentials. Annotation that in Windows Server 2012 and Windows Server 2012 R2, however, the Trusted Platform Module (TPM) of client computers can human activity equally a virtual smart card for two-factor authentication.
Alternatively, you tin can too configure two-gene hallmark so that users must enter an OTP such equally i provided through RSA SecurID in addition to their Active Directory credentials. OTP requires a PKI and RADIUS server, along with a number of configuration steps that y'all don't demand to understand for the lxx-417 exam. For the lxx-417 test, you lot merely demand to know that OTP is an alternative to smart cards for two-gene authentication in DirectAccess.
- Utilise Reckoner Certificates If you configure DirectAccess in the GUI, customer computers are authenticated through Kerberos by default. However, you tin can select an choice to crave computer authentication through the use of certificates. Estimator certificate authentication is required to support two-factor authentication, a multisite deployment of DirectAccess, or Windows 7 DirectAccess clients.
- Enable Windows 7 Client Computers To Connect Via DirectAccess By default, Windows 7 customer computers cannot connect to a Windows Server 2012 or Windows Server 2012 R2 Remote Access deployment. Y'all need to enable that functionality hither.
-
Enable Corporate Compliance For DirectAccess Clients With NAP This page allows y'all to require a health check of client computers through NAP. To configure this setting in Windows PowerShell, use the Set-DAServer cmdlet with the -HealthCheck parameter.
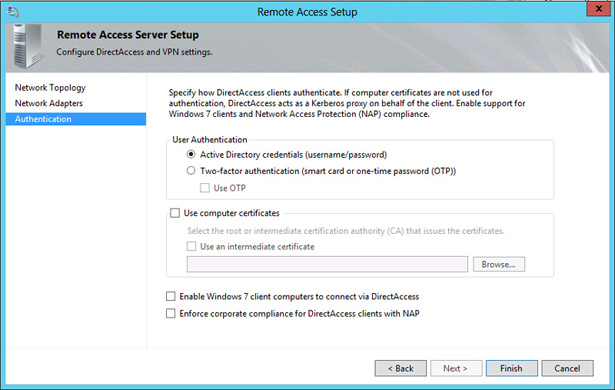
FIGURE 6-fourteen The Authentication page of the Remote Admission Server Setup Magician
Pace 3: Infrastructure Server Setup
The Infrastructure Server Setup Wizard allows you to configure settings related to the network location server, the DNS server, and management servers such as update or antivirus servers.
The first page of this magician is the Network Location Server page, shown in Figure half-dozen-15. As explained earlier in this affiliate, DirectAccess clients use this server to make up one's mind whether they are on the company network. It'due south recommended that you use an internal web server other than the DirectAccess (Remote Access) server for this purpose. (The DNS address and associated IP accost in this case is naturally associated with the interface fastened to the internal network.) If you do specify the DirectAccess server every bit the network location server, information technology must be authenticated by a calculator certificate—a self-signed one, if necessary. To configure the network location server using Windows PowerShell, use the Gear up-DANetworkLocationServer cmdlet.
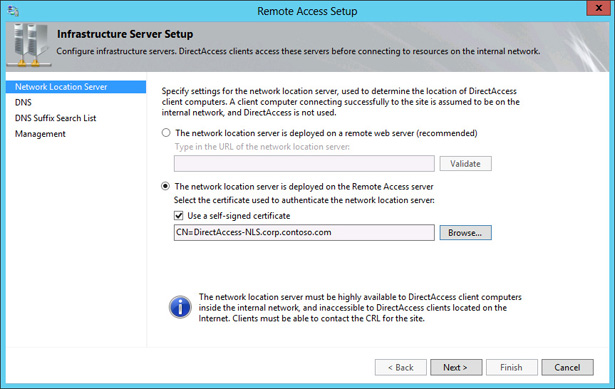
FIGURE 6-xv The Network Location Server page of the Infrastructure Server Setup Wizard
The second page of the Infrastructure Server Setup Wizard is the DNS page shown in Effigy six-xvi. The master role of this page is to allow y'all to configure the Proper name Resolution Policy Tabular array (NRPT). The entries you create here are written to the GPO used to configure DirectAccess clients.
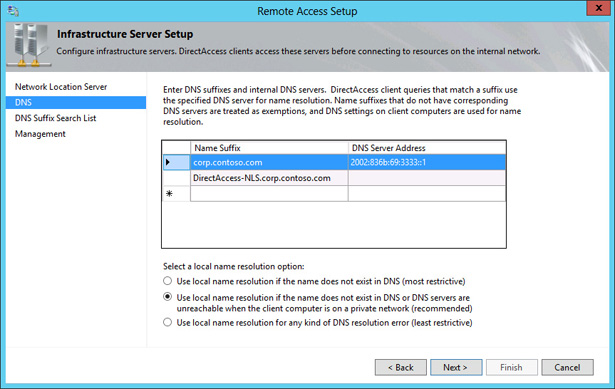
Effigy 6-sixteen The DNS folio of the Infrastructure Server Setup Sorcerer
The NRPT is a feature that allows a DNS client to assign a DNS server address to particular namespaces rather than to particular interfaces. The NRPT essentially stores a list of name resolution rules that are practical to clients through Grouping Policy. Each dominion defines a DNS namespace (a domain name or FQDN) and DNS customer behavior for that namespace. Together, these name resolution rules are called a Name Resolution Policy. When a DirectAccess client is on the Cyberspace, each proper noun query request is compared confronting the namespace rules stored in the Name Resolution Policy. If a match is found, the request is processed according to the settings in the Name Resolution Policy dominion. The settings decide the DNS servers to which each request will exist sent. If a name query request does not match a namespace listed in the NRPT, information technology is sent to the DNS servers configured in the TCP/IP settings for the specified network interface.
You might need to configure Proper noun Resolution Policy entries if, for example, you need to enable DNS clients to resolve DNS suffixes institute only within your intranet namespace. Some other reason might be if you have a split public/private DNS surroundings based on the aforementioned domain name, and yous demand to ensure that DirectAccess clients don't contact your company's public servers (such as a spider web server) through the DirectAccess connexion.
The 2nd configuration decision you need to make on the DNS page relates to the DirectAccess clients' use of local proper name resolution methods such equally NetBIOS and LLMNR. Unlike the setting in the DirectAccess Client Setup Magician, which merely allows (does not block) the use of local proper name resolution, the setting here determines how local proper noun resolution will be used if allowed. Y'all accept three options. The most restrictive is to employ local name resolution only if the name does not exist in DNS. This choice is considered the near secure considering if the intranet DNS servers cannot be reached, or if there are other types of DNS errors, the intranet server names are not leaked to the subnet through local proper noun resolution. The 2d and recommended pick is to apply local proper name resolution if the proper name doesn't exist in DNS or DNS servers are unreachable when the client computer is on a private network. The concluding and least restrictive option is to use local name resolution for any kind of DNS resolution error. This choice is considered the to the lowest degree secure because the names of intranet network servers can be leaked to the local subnet through local proper name resolution.
To configure local name resolution for clients in Windows PowerShell, employ the Set-DAClientDNSConfiguration cmdlet with the -Local parameter. The iii choices available in the GUI are designated by the FallbackSecure, FallbackPrivate, or FallbackUnsecure values, respectively.
The third folio of the Infrastructure Server Setup Wizard is the DNS Suffix Search List Folio, shown in Effigy half dozen-17.
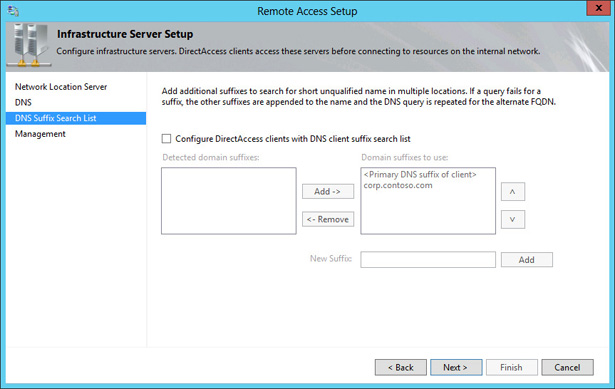
Figure six-17 The DNS Suffix Search List page of the Infrastructure Server Setup Magician
DirectAccess clients utilize the list you lot configure here to resolve single label names, such as http://finance. DNS cannot resolve single label names unless the DNS client first appends a suffix or if a GlobalNames zone is in utilize on the DNS servers. Past default, the suffix is the domain to which the computer is joined.
The fourth and final folio of the Infrastructure Server Setup Wizard is the Direction folio, shown in Figure 6-18.
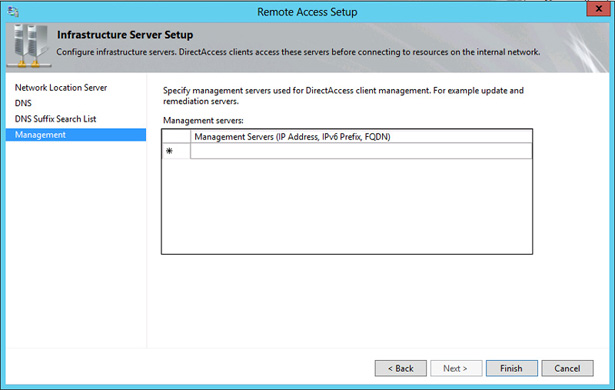
FIGURE 6-xviii The Management page of the Infrastructure Server Setup Magician
You don't demand to enter any domain controllers or Configuration Manager servers here because they are automatically detected the get-go time that DirectAccess is configured. Instead, apply this page to configure DNS clients with the names of management servers that cannot be detected automatically, such as Windows Server Update Services (WSUS) update servers and antivirus servers. Note that if the list of available domain controllers or Configuration Managing director servers is modified afterward yous configure DirectAccess, you can only click Update Management Servers in the Remote Admission Management Console to refresh the management server listing.
In that location is one other point to be aware of: Management servers that initiate connections to DirectAccess clients must support IPv6 either natively or through ISATAP.
Step iv: DirectAccess Application Server Setup
DirectAccess Application Server Setup is a single configuration folio, as shown in Figure 6-xix. You can use this page to configure encryption between the application servers you specify here and the DirectAccess server. (By default, of course, traffic is already encrypted between the DirectAccess client and server.)
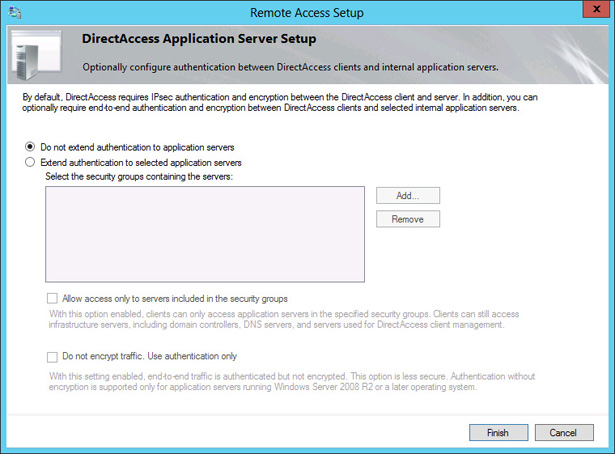
Figure half dozen-19 The DirectAccess Awarding Server Setup page
To configure the list of awarding servers using Windows PowerShell, use the Add-DAAppServer cmdlet.
Step 5: Advanced configuration options
After you complete DirectAccess Application Server Setup, the Remote Admission Management Console appears, as shown in Effigy 6-20. At this bespeak, you tin can start new wizards to configure advanced options such as a multisite deployment or load balancing past clicking the related options in the Tasks pane.
Verifying the configuration
Afterward you lot take completed your configuration, you can utilise the Operations Status item in the left pane of the Remote Access Management Console to verify that DirectAccess is gear up to use. Remote clients tin can begin to connect to the network through DirectAccess later the operations status off all components is shown to exist working, every bit shown in Figure 6-21. This procedure can take several minutes or more after you complete the last configuration sorcerer.
After the server components are working, you can verify DirectAccess functionality from the client cease. Get-go, you can utilise the Get-DAConnectionStatus cmdlet to determine whether DirectAccess can properly determine the location of the client. Figure 6-22 shows a Windows PowerShell console session from a portable client that is initially plugged in to a corporate network. The commencement time the cmdlet is run, the customer is shown to exist continued locally. When the laptop is disconnected and an Internet broadband connection is enabled, the cmdlet is run over again. This time, the client is determined to be connected remotely, and connectivity to the intranet is established through DirectAccess. Some other manner to verify DirectAccess functionality on the client end is to expect at the connection status in the Networks bar. Effigy six-23 shows how a DirectAccess connection appears when it is available.
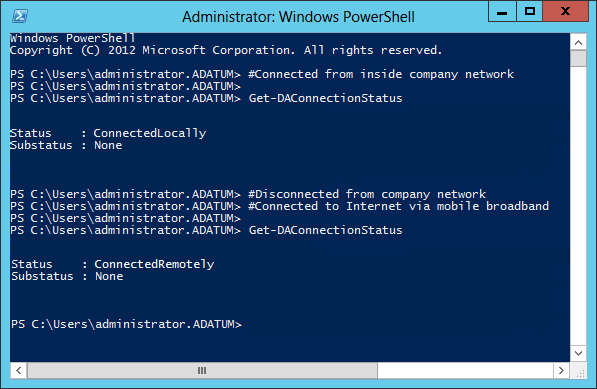
FIGURE half dozen-22 DirectAccess automatically determines when a client is continued locally or remotely

FIGURE 6-23 A DirectAccess connection as it appears in the Networks bar in Windows 8
Discover that the icon representing a DirectAccess connection in Figure 6-23 resembles a server. Dissimilarity this DirectAccess icon with the VPN icon shown in Figure 6-24. These icons were showtime introduced in Windows Server 2012 and Windows viii. You need to be able to recognize both the DirectAccess and VPN icons for the 70-417 exam.

FIGURE six-24 A VPN connectedness as it appears in the Networks bar in Windows viii
Objective summary
- DirectAccess is a bidirectional, always-on culling to a VPN that clients can employ to connect to corporate resources while they are connected to the Internet. DirectAccess get-go appeared as a feature in Windows Server 2008 R2 and Windows 7, but since the release of Windows Server 2012 and Windows 8, DirectAccess deployment has been greatly simplified.
- Windows Server 2012 and Windows eight removed the requirement that DirectAccess clients cosign themselves through computer certificates. Instead, Kerberos now is used as the default option.
- Windows Server 2012 introduced several new infrastructure and topology options for DirectAccess, including support for multiple domains, support for multiple sites, deploying the DirectAccess server behind a NAT device, and load balancing through an NLB cluster.
-
In Windows Server 2012, DirectAccess and VPNs were unified in a new server role named Remote Access. To add the DirectAccess component of the Remote Access role, type the following at an elevated Windows PowerShell prompt:
Install-WindowsFeature DirectAccess-VPN -IncludeManagementTools
- Y'all can configure DirectAccess by completing four wizards corresponding to DirectAccess clients, the DirectAccess server, infrastructure servers, and application servers. These wizards include a number of features and options that tin plausibly appear in test questions on the 70-417 exam. For this reason, information technology is recommended that yous learn about all of the options in these wizards to prepare for the test.
Objective review
Answer the following questions to test your knowledge of the information in this objective. You lot can find the answers to these questions and explanations of why each answer choice is right or incorrect in the "Answers" section at the end of the chapter.
-
Which of the following is required to establish a DirectAccess connection betwixt a Windows 8.i customer and a DirectAccess server running Windows Server 2012 R2?
- A estimator certificate on the client.
- A user certificate on the client.
- An IPv6 address on the customer.
- An IPv4 address on the customer.
-
Yous are an administrator for a company with a network that includes 300 computers running Windows viii.1 and 20 servers running Windows Server 2012 R2. The network consists of a single domain named Contoso.com.
Your manager has asked you to begin testing DirectAccess with a group of 20 trial users in your organization. You deploy a single DirectAccess server on the visitor network edge and choose to implement computer authentication through Kerberos. You later inquire the trial users to try to connect to the corporate network from exterior the visitor premises. All users attempt to connect on domain-joined computers running Windows eight.1. Although well-nigh users are able to connect remotely to the corporate network, certain users working on desktop computers or virtual machines report that they cannot plant a connexion. Y'all would like to enable these users to connect to the corporate network through DirectAccess.
Which of the following Windows PowerShell commands is near probable to help you meet your goal?
- Set up-DAClient -OnlyRemoteComputers "Enabled"
- Set-DAClient -OnlyRemoteComputers "Disabled"
- Prepare-DAClient -ForceTunnel "Enabled"
- Prepare-DAClient -ForceTunnel "Disabled"
-
You are an administrator for a company named Contoso.com with a network that includes 500 computers running Windows 8.1 and 30 servers running Windows Server 2012 R2. The network consists of a unmarried domain named Contoso.com.
Many Contoso employees work on the road and only rarely visit the company premises. They currently connect to the company network by ways of a VPN. You desire to deploy DirectAccess so that you can use software patches through Arrangement Center Configuration Manager. Yous don't want to enable computers to access resources on the company network through the DirectAccess connection.
Which of the following Windows PowerShell commands volition help you lot meet your goal?
- Ready-DAServer -DAInstallType ManageOut
- Gear up-DAServer -DAInstallType FullInstall
- Set up-DAServer -HealthCheck "Enabled"
- Set-DAServer -HealthCheck "Disabled"
Source: https://www.microsoftpressstore.com/articles/article.aspx?p=2216993
Post a Comment for "Review Windows Server 2012r2 What Are Some of the Key Remote Access Services"